Referred URL
http://lifehacker.com/5875162/how-often-should-i-charge-my-gadgets-battery-to-prolong-its-lifespan

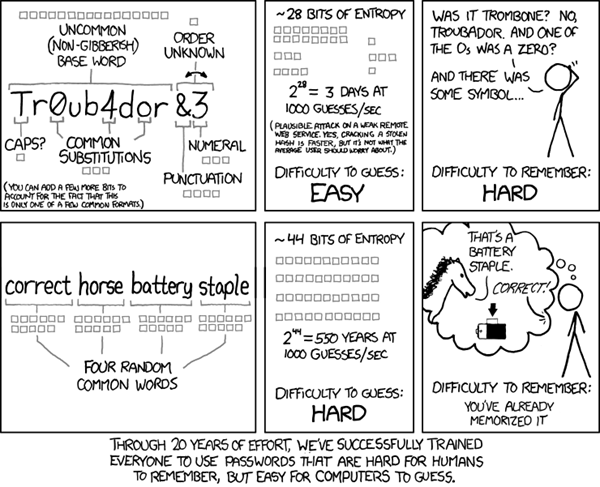
Most lithium batteries should last you a few years, but improper care can decrease that lifespan, meaning that your battery will be unable to hold a charge—or unable to hold as big a charge as it used to—quicker. So, to clear things up, here's how to actually extend your battery's health as much as possible.
-

- Perform shallow discharges. Instead of discharging to 0% all the time, lithium-ion batteries do best when you discharge them for a little bit, then charge them for a little bit. The table at the right, from Battery University, shows that discharges to 50% are better for your battery's long-term life than, say, small discharges to 90% or large discharges to 0% (since the 50% discharges provide the best number of cycles-to-usage ratio).
- Don't leave it fully charged. Similarly, lithium-ion batteries don't need to be charged all the way to 100%. In fact, they'd prefer not to be—so the 40%-80% rule you heard is a good guideline. When possible, keep it in that range to prolong its life as long as you can. And, if you do charge it to 100%, don't leave it plugged in. This is something most of us do, but it's another thing that will degrade your battery's health. If you need to charge it overnight, use something like the Belkin Conserve Socket to stop it from charging after it's full.
- Fully discharge it once a month. This may seem contradictory, but hear us out. While lithium-ion batteries shouldn't be discharged regularly, most modern batteries are what's known as "smart batteries", which means that they can tell you how long you have until your battery dies (e.g. "2 hours, 15 minutes remaining"). This feature can get miscalibrated after a lot of shallow discharges. So, manufacturers recommend fully discharging your battery once a month to make sure this stays accurate.
-




 It flat sucks to lose your phone.
It flat sucks to lose your phone.